Did you know?
86% of security breaches are envidenced in log files but only
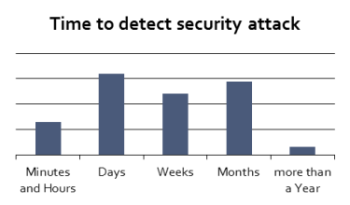
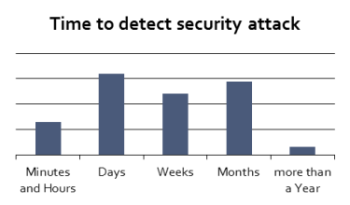
13% of attacs are detected within 24 hours.
86% of security breaches are envidenced in log files but only
13% of attacs are detected within 24 hours.
Humans are better processors of visual information than text. Novel visualizations enable humans to sort through huge amounts of log file data to apply our best asset, visual pattern recognition, to detect anomolous behaviors.
Please watch the video below for a demonstration of InViz's concepts and capabilities